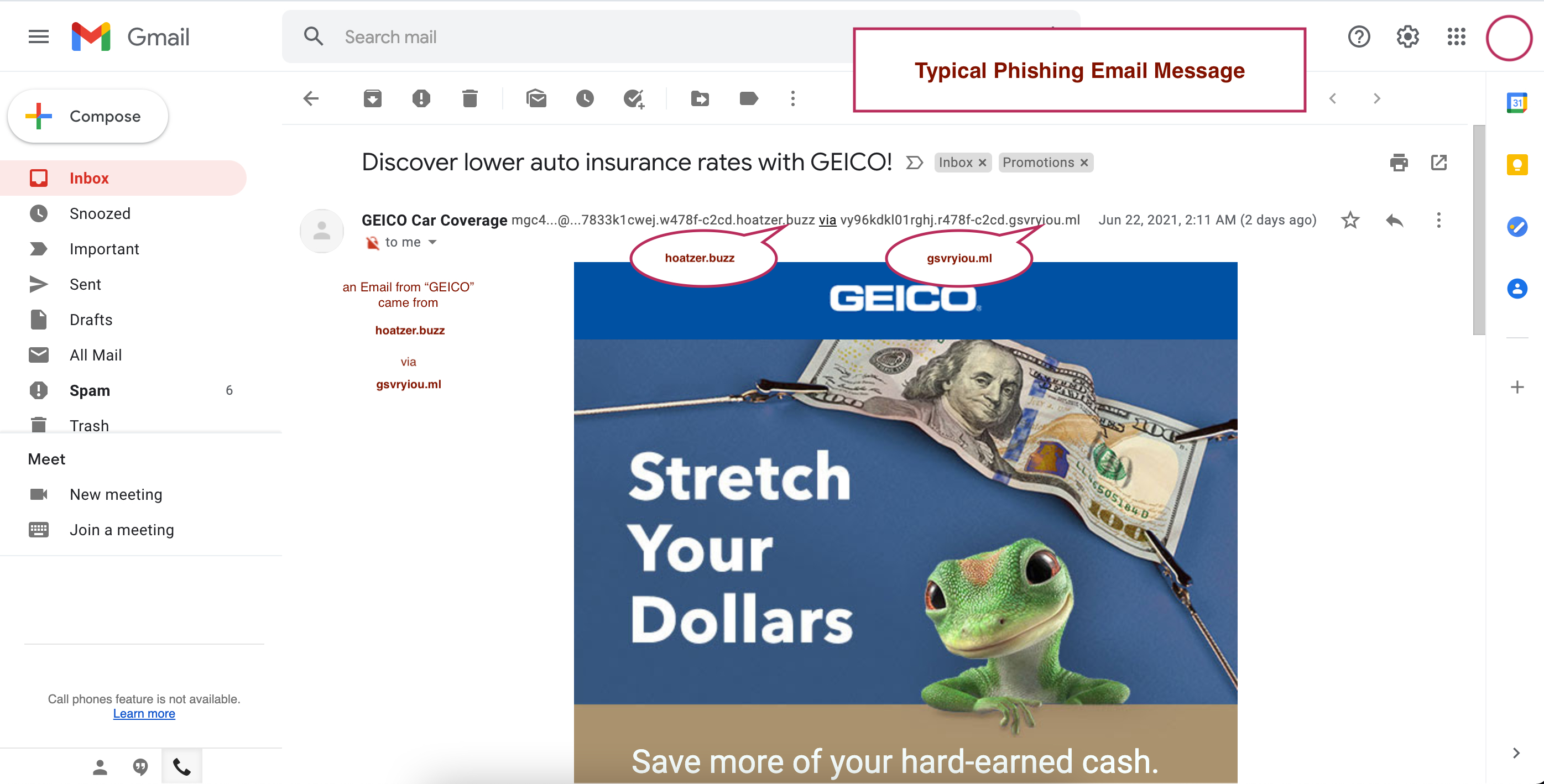
The session will examine how AI-powered phishing, business email compromise, and ransomware campaigns are becoming more targeted and harder...
Extortionware exposed: Attacks up ante on businesses | The Arkansas Democrat-Gazette
Just a few years ago, ransomware followed a relatively simple script. Criminals broke into a company's network, locked up its data thro...
Cookeville Regional Medical Center hospital data breach impacts 337,917 people
A ransomware attack on a Tennessee hospital exposed data of 337000 people after hackers stole 500GB of sensitive information. by Google A...
Ransomware reaches elevated 'new normal' as attack volumes hold steady into 2026 ...
In its report titled ' Ransomware and Cyber Threat Insights,' the GuidePoint Research and Intelligence Team (GRIT) identified that ...
6-Year Ransomware Campaign Targets Turkish Homes & SMBs - Dark Reading
Ransomware Against Turkish SMBs. The phishing flow used for this campaign is hardly that interesting, perhaps because it doesn't have t...
ZAWYA: Veeam report reveals a market-wide shift from recovery confidence - TradingView
... ransomware attackDUBAI, UAE, 15TH April, 2026 — Veeam® Software, the Data and AI Trust Company, today released the Data Trust and Resil...
Ababil of Minab claims cyberattack on LACMTA, exposing risks to rail control systems and ...
A compromise at this level would provide attackers with the ability to disrupt large numbers of virtual machines, deploy ransomware at scal...
The Week in Breach News: April 15, 2026 | Kaseya
Stay one step ahead of threats with the latest insights and defense strategies. Understanding phishing: How a ransomware attack unfolds. Un...
Halcyon Opens New Office in Austin, Expanding Innovation Hub to Advance the Fight ...
... ransomware platform designed to defeat ransomware and strengthen resilience against modern cyber threats. About Halcyon. Halcyon, the ...
Spring Lake Park Schools Shut Down After Suspected Ransomware Attack - National Today
This incident underscores the growing threat of ransomware attacks targeting schools and the potential for widespread disruption to educati...
Hackers Give Rockstar Games Until April 14 To Pay For Stolen Data - Forbes
A notorious group of ransomware hackers has added Rockstar Games to its list of victims on the dark web leak site used to promote successfu...
Security Affairs newsletter Round 572 by Pierluigi Paganini – INTERNATIONAL EDITION
... Ransomware attack on ChipSoft knocks EHR services offline across hospitals in the Netherlands and Belgium · UAT-10362 linked to LucidRo...
A German hacker involved in a cryptocurrency ransomware case was arrested in Bangkok ...
Investigations reveal that he is suspected of developing and operating a ransomware platform and a "Cybercrime as a Service" (Caa...
Winona County Enlists National Guard, BCA After Second Cyberattack - Rochester Today
... ransomware attack. The county is working to restore its systems in phases, verifying each one's security before bringing it back on...
The Winona County Sheriff's Office is sharing updates on a ransomware incident. FULL STORY
A former daycare worker, Theah Russell, is now indicted on first-degree premeditated murder charges in the death of 11-month-old Harvey Mukl...
Deepfake-As-A-Service Is The New Ransomware-As-A-Service - RamaOnHealthcare
You've heard of ransomware -as-a-service. Most executives have by now. An attacker buys the malware off the shelf, deploys it, collects ...
Enhancing dental practice cybersecurity on a budget | DrBicuspid.com
Exploiting these technical vulnerabilities is the second most common methodology that hackers use to deliver ransomware . By addressing the ...
Cybersecurity and Data Privacy - Dykema
Prioritize ransomware resilience and escapes from extortion: Build incident response plans that address production shutdowns, fleet immobil...
Microsoft Links Medusa Ransomware Affiliate to Zero-Day and N-Day Exploits in Rapid Attacks
What happened Microsoft said Storm-1175, a China-based financially motivated threat group known for deploying Medusa ransomware , has been u...
Germany Doxes “UNKN,” Head of RU Ransomware Gangs REvil, GandCrab
An elusive hacker who went by the handle "UNKN" and ran the early Russian ransomware groups GandCrab and REvil now has a name and...