As many other applications use Log4j, threat actors quickly used the "Log4Shell" vulnerability in cyberattacks to deploy ransomware, install the ...
Popular
-
... FBI identifying the threat actor as "Scattered Spider", a sophisticated cybercriminal group known for data extortion and ranso...
-
Ransomware : Ransomware attacks rose by 37% since last year, and are now present in 44% of breaches, despite a noticeable decrease in the m...
-
Some Exchange Server bugs: Let attackers run malicious scripts, sometimes leading to ransomware . Log4j vulnerability: A vulnerability in a ...
-
Ransomware sneakily steals Discord login tokens before opening a ransom note with no mention of the theft. From Google Alert - ransomwar...
-
The Ransomware Decade: The Creation of a Fine-Grained Dataset and a Longitudinal Study. Authors: Armin Sarabi, Ziyuan Huang, Chenlan Wang, ...
-
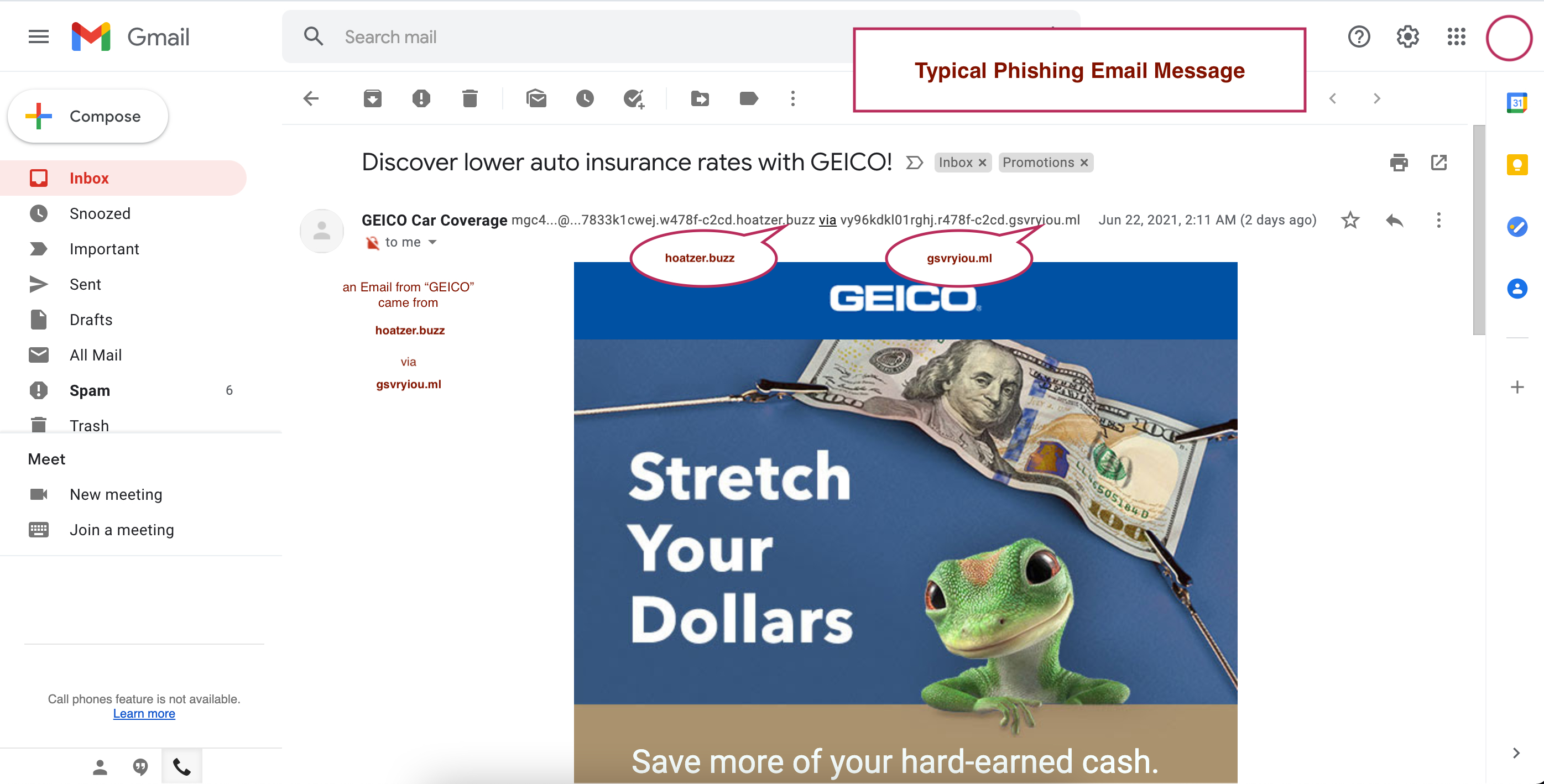
The Phishing Email problem Email Headers show that the message did not come from the claimed sender The best solutions to fi...
-
In a rather clever attack, hackers leveraged a weakness that allowed them to send a fake email that seemed delivered from Google's syste...
Featured Article
Typical Phishing Email
The Phishing Email problem Email Headers show that the message did not come from the claimed sender The best solutions to fi...