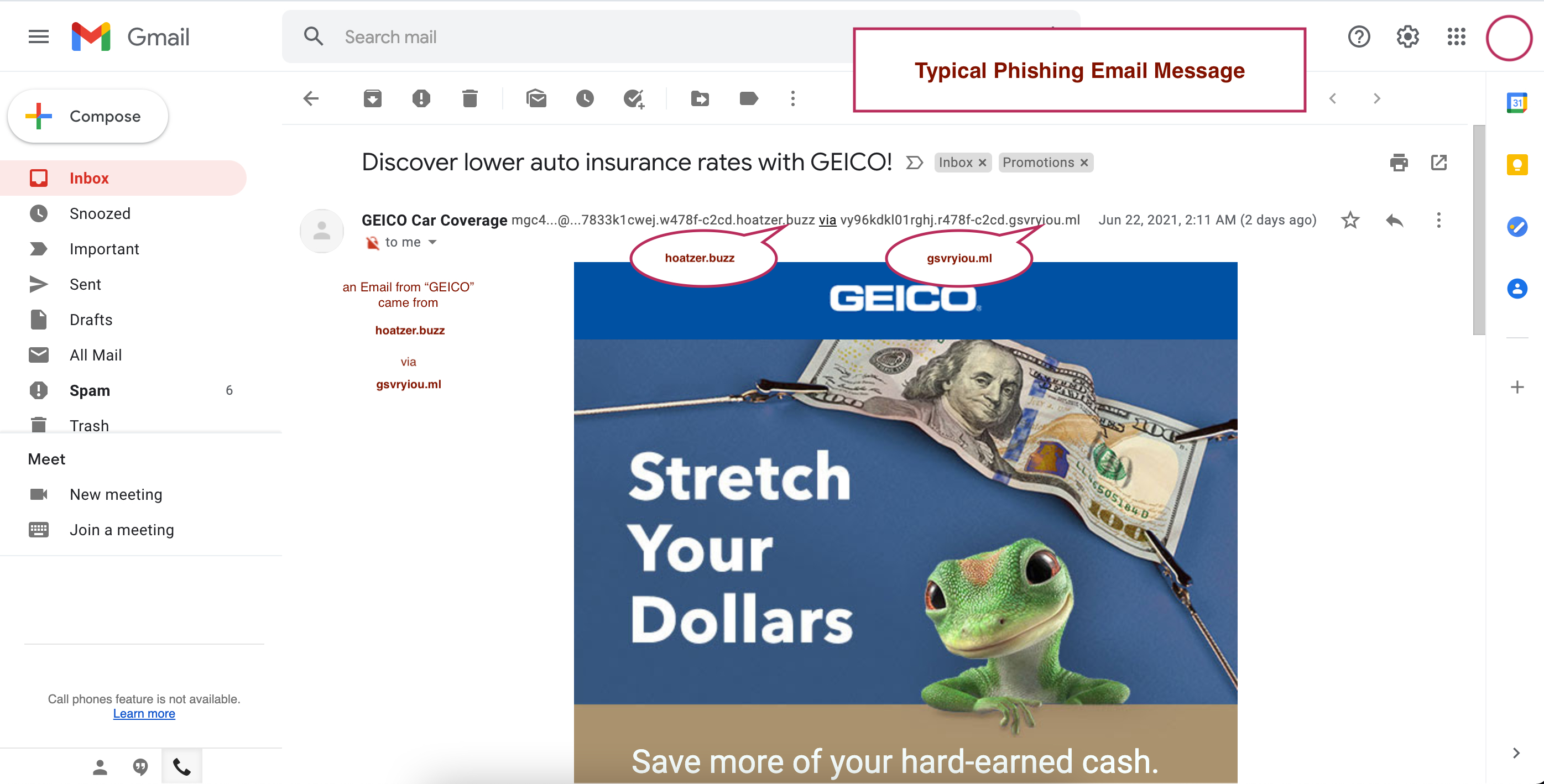
Khudaverdyan gained access to T-Mobile's internal computer systems using credentials stolen in phishing attacks from more than 50 different T-Mobile employees.
The stolen credentials were used to access T-Mobile's internal computer systems, and, in many cases, for password resets which locked the account owners out of the system.
Working with others in overseas call centers, Khudaverdyan also received T-Mobile employee credentials which he then used to access T-Mobile systems to target higher-level employees by harvesting those employees’ personal identifying information and calling the T-Mobile IT Help Desk to reset the employees’ company passwords, giving him unauthorized access to the T-Mobile systems which allowed him to unlock and unblock cellphones," US DOJ said in an August press release when Khudaverdyan pleaded guilty.
Throughout the scheme, they advertised "direct premium unlocking services for all phone carriers" to potential customers through various means, including emails and dedicated websites.
Using the stolen credentials and the IMEI numbers sent by customers through the websites they controlled, the two men unlocked hundreds of thousands of Android and iOS devices using T-Mobile's dedicated Mobile Device Unlock (MDU) and MCare Unlock (MCare) tools.
The sentencing hearing is scheduled to take place in two months, on February 23, 2023.
The stolen credentials were used to access T-Mobile's internal computer systems, and, in many cases, for password resets which locked the account owners out of the system.
Working with others in overseas call centers, Khudaverdyan also received T-Mobile employee credentials which he then used to access T-Mobile systems to target higher-level employees by harvesting those employees’ personal identifying information and calling the T-Mobile IT Help Desk to reset the employees’ company passwords, giving him unauthorized access to the T-Mobile systems which allowed him to unlock and unblock cellphones," US DOJ said in an August press release when Khudaverdyan pleaded guilty.
Throughout the scheme, they advertised "direct premium unlocking services for all phone carriers" to potential customers through various means, including emails and dedicated websites.
Using the stolen credentials and the IMEI numbers sent by customers through the websites they controlled, the two men unlocked hundreds of thousands of Android and iOS devices using T-Mobile's dedicated Mobile Device Unlock (MDU) and MCare Unlock (MCare) tools.
The sentencing hearing is scheduled to take place in two months, on February 23, 2023.